SMARTQUERY: An Active Learning Framework for Graph Neural Networks through Hybrid Uncertainty Reduction
Xiaoting Li, Yuhang Wu, Vineeth Rakesh Mohan, Yusan Lin, Hao Yang and Fei Wang
Driven by the pursuit of creating the future of payments for everyone, everywhere through scientific innovation, Visa Research conducts fundamental and applied research on challenging problems in the payment industry and provide technical thought leadership for Visa's future.

Visa Research receives Special Recognition Award
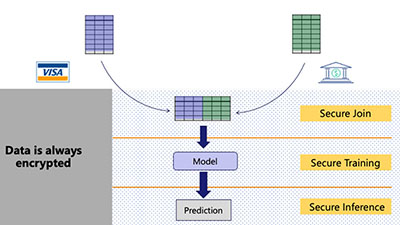
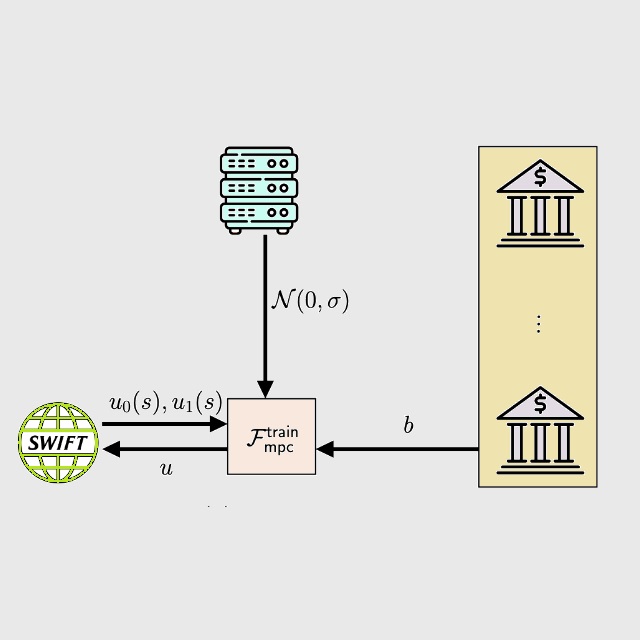
Privacy, Security, Machine Learning
Helps financial institutions issue and manage fiat-backed tokens on blockchain networks.
Blockchain, Digital Currencies, Cryptography

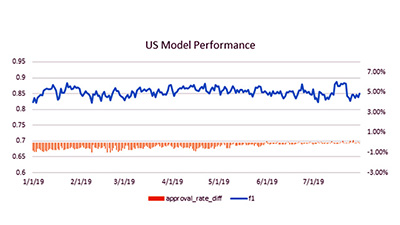
Stand-in processing enhanced by deep learning
Artificial Intelligence, Deep learning
Visa Research receives Best Paper Honorable Mentions and Best Visualization Notes awards
Explainable Artificial Intelligence, Visualization
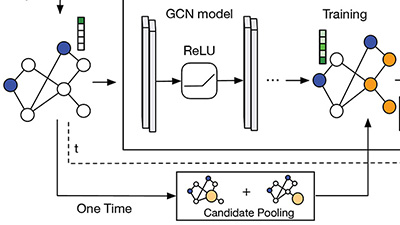
Xiaoting Li, Yuhang Wu, Vineeth Rakesh Mohan, Yusan Lin, Hao Yang and Fei Wang
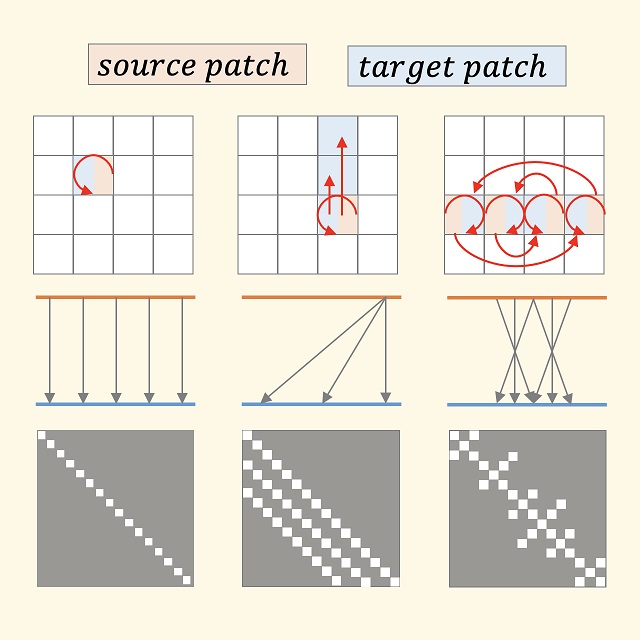
Prince Aboagye, Yan Zheng, Michael Yeh, Junpeng Wang, Zhongfang Zhuang, Huiyuan Chen, Liang Wang, Wei Zhang, Jeff Phillips
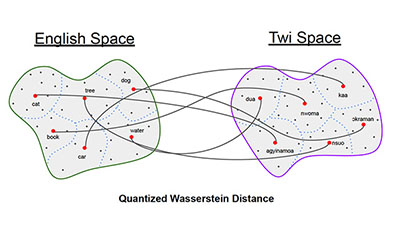
Huiyuan Chen, Yusan Lin, Menghai Pan, Lan Wang, Chin-Chia Michael Yeh, Xiaoting Li, Yan Zheng, Fei Wang, Hao Yang
Huiyuan Chen, Xiaoting Li, Kaixiong Zhou, Xia Hu, Chin-Chia Michael Yeh, Yan Zheng, Hao Yang
Collaboration is key at Visa. At Visa Research, we collaborate with thought leaders, pioneers, some of the world’s most inspired thinkers, and industry leaders to help us uncover insights into the future of payments.